If you are a Salesforce admin or an IT manager managing salesforce, one of the issues which always happens is the certificate warning message which triggers an email to all the Users creating panic. The impact of these certificates expiry could be pretty devastating if you are using single sign-on which would cause logins to fail to result in shutting down Salesforce. So the question is How do you manage this effectively and avoid the potential disaster?
Proactively identify potential impact.
Once you get the self-signing certificate warning by email on screen, you need to identify where the certificate is used. Self-signed certificates are used in the following areas of salesforce.
- Single Sign-on with your Identify provider
- Outbound messages
- Custom code.
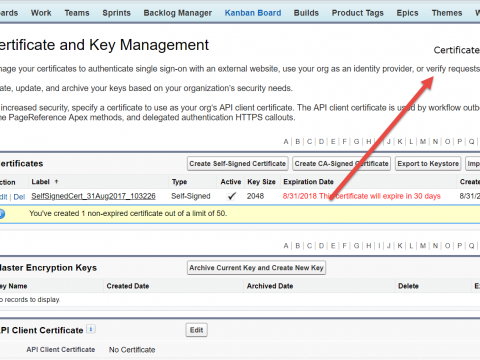
Once you identify the areas of impact, you can easily identify the solutions to fix the problem. See the below screenshot to see if the certificate is used in API calls.
The below screenshot will help you to find whether your self-signed certificate is used on single sign-on configurations.
Solve the problem.
Once you identify where all your certificate is used, you can then decide how to solve the problem quickly. Here is what you do to fix it as next step.
- Generate a new self-signed certificate. Now when you generate the certificate, always make sure that you choose the key size as 4096 which will make the certificate last for 2 years. The below screenshot shows an example of this.
- Once you create it, you can test this on a sandbox based on the following limitations.
- You can create a separate sign-on connected app and test it with certain profiles in production.
- If your single sign-on settings use email id as a subject, you can create a new user in the sandbox with a user who has never used salesforce. You can log in as that user and test his single sign on.
- After you have tested it, you can deploy this in production and ensure single sign-on works with all users. To verify your testing is working, you need to check the login history to verify users are using the single sign-on for testing.
Prevent future problems.
Once you have resolved the certificate expiry issue, there are things you can do the prevent this in future.
- I would recommend using a CA-signed certificate than a self-signed certificate because it will last more than 2 years and you do not need to worry about certificate expiry every time.
- Have a yearly review week where your support team checks for certificates expiring as one of their tasks at the end of the year.
- Single sign-on certificates send warning emails to all your users before 30 days, one day before expiry and during expiration. So in order to prevent this warning email, you need to make sure that not all your users have modify all data permission. If all your users get this warning email, there is a different problem which is all your users have modify all data permission which needs to resolved right away!!! 🙄
So to summarize, self-signing certificates are essential to make your single sign-on work. But here is your top 3 takeaways.
- Create self-signing certificates for last 2 years minimal.
- Work on self-signing certificates 15 days advance to the expiration date rather than locking out all users.
- Use a CA-signed certificate to avoid this support issue a long time.
As always please feel free to email me your thoughts and post your comments below!! You can always email me at buyan@eigenx.com for further questions.